How x86 Jumps REALLY Work: EFLAGS Truth with GDB + pwndbg
All x86 conditional jumps (ja, jb, je, etc.) are triggered by EFLAGS — not by syntax or code order. Hands-on with GDB and pwndbg to see exactly which flag fires each branch.
Long-form video on kernel debugging (GDB / QEMU / Yocto), eBPF, bootloaders, assembly, memory models, and runtime internals.
All x86 conditional jumps (ja, jb, je, etc.) are triggered by EFLAGS — not by syntax or code order. Hands-on with GDB and pwndbg to see exactly which flag fires each branch.
Hand-written Stage-1 bootloader in raw x86 assembly. No GRUB, no operating system, no standard library. Boots directly from BIOS.

Join me on a tour of my security lab, where I explore the evolution of operating systems from FreeDOS to modern AI-driven security research.
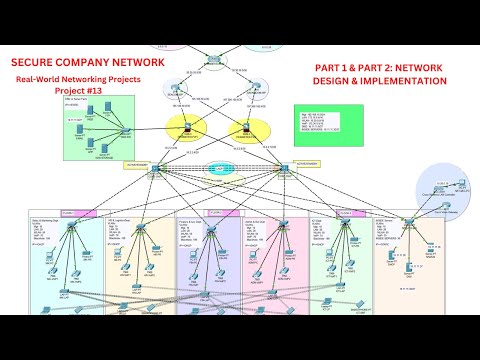
A comprehensive 3-hour demonstration of how to design and implement a secure enterprise network with multiple security zones, VLANs, and proper firewall configuration

This is one of the clearest demonstrations of a buffer overflow attack I've seen, where Dr. Mike Pound not only explains the theory but shows the complete attack process, invaluable for security learners
© 2026 HarrisonSec. All rights reserved.