[ Videos ]
Video hub — watch → notes → code

Why Claude Code's Agent Loop Is 1,421 Lines
A deep dive into query.ts — the 1,729-line async generator at the heart of Claude Code. 10 steps per iteration, 9 continue points, 4-stage compression, streaming tool execution, and error recovery. The engine behind every AI coding agent.
Watch Video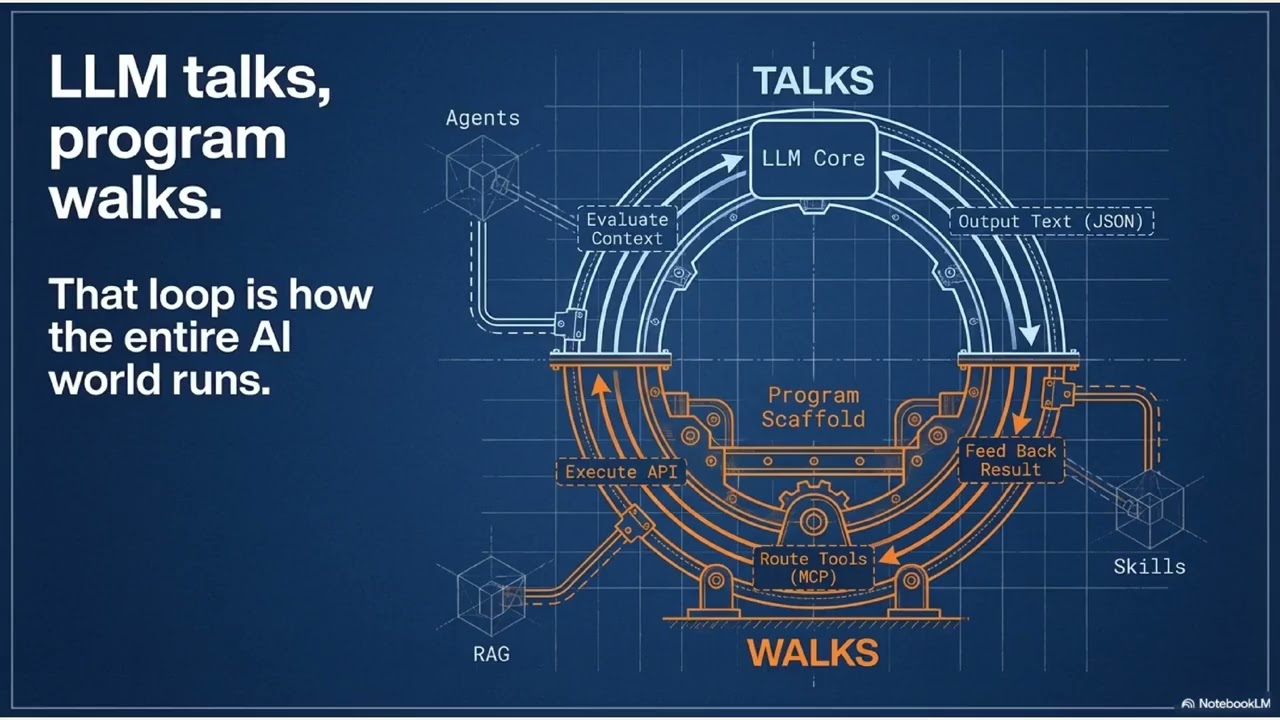
The AI Stack Explained: LLM Talks, Program Walks
A first-principles breakdown of the entire AI stack in 15 minutes — from LLM to Agent. One mental model: the LLM can only output text, the program does everything else.
Watch Video
HarrisonSec Lab Tour | A Journey Through Computing Evolution
Join me on a tour of my security lab, where I explore the evolution of operating systems from FreeDOS to modern AI-driven security research.
Watch Video
StegoSafe: Hiding Secrets in Images with Encryption and Secret Sharing
A quick demo of StegoSafe's web version, showing how to encrypt, split, and hide secrets inside images using advanced steganography.
Watch Video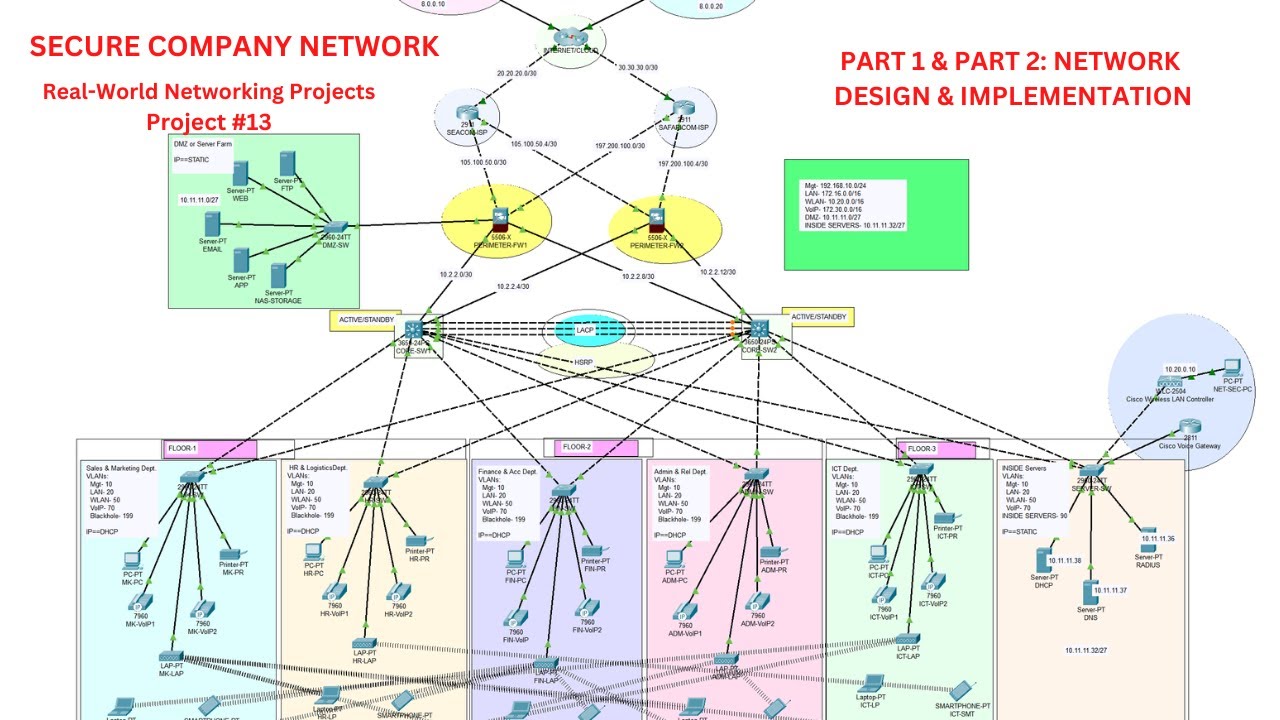
Complete Secure Company Network Design
A comprehensive 3-hour demonstration of how to design and implement a secure enterprise network with multiple security zones, VLANs, and proper firewall configuration
Watch Video
Buffer Overflow Attack Explained
This is one of the clearest demonstrations of a buffer overflow attack I've seen, where Dr. Mike Pound not only explains the theory but shows the complete attack process, invaluable for security learners
Watch Video